publications
2026
-
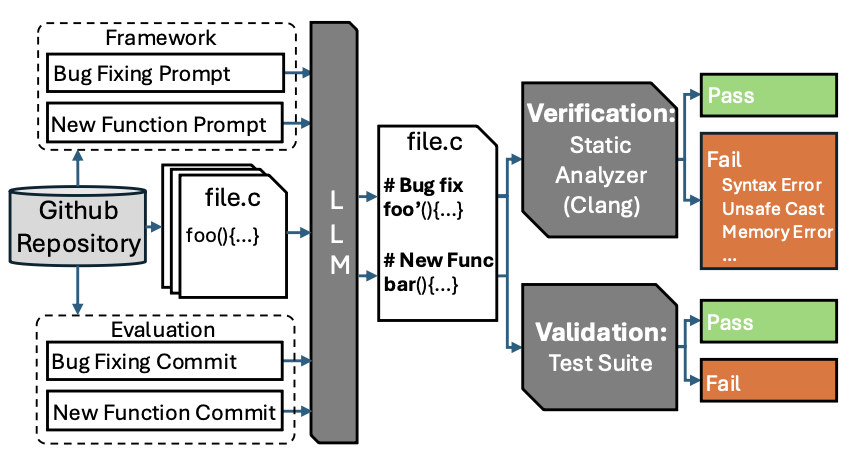 Can LLMs be Effective Code Contributors? A Study on Open-source ProjectsAccepted to International Conference on Evaluation and Assessment in Software Engineering (EASE), 2026
Can LLMs be Effective Code Contributors? A Study on Open-source ProjectsAccepted to International Conference on Evaluation and Assessment in Software Engineering (EASE), 2026
2025
-
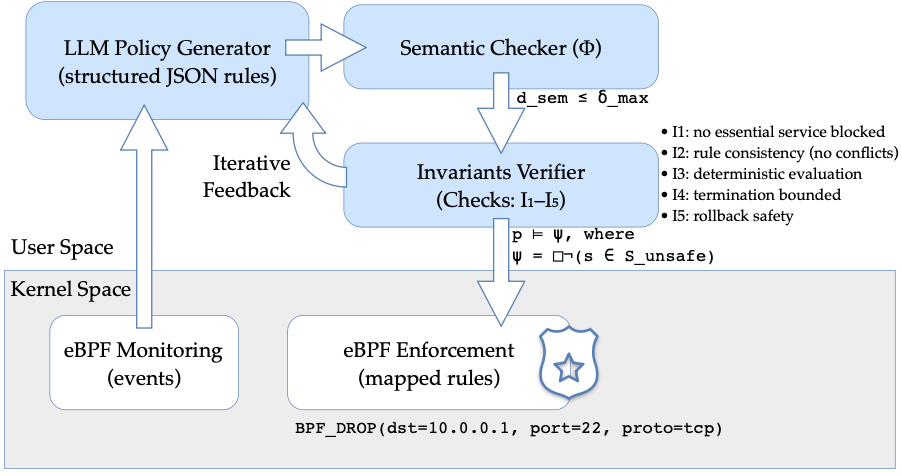 PACE: Policy Adaptation for Cybersecurity Events Through Formal Verification of LLM-Generated Firewall PoliciesIn Proc. IEEE BigData (CyberHunt Workshop), 2025
PACE: Policy Adaptation for Cybersecurity Events Through Formal Verification of LLM-Generated Firewall PoliciesIn Proc. IEEE BigData (CyberHunt Workshop), 2025 -
-
 NUSGuard: Smart Device Anti-Eavesdropping Protection based on Near-Ultrasonic InterferenceIEEE Transactions on Information Forensics and Security, 2025
NUSGuard: Smart Device Anti-Eavesdropping Protection based on Near-Ultrasonic InterferenceIEEE Transactions on Information Forensics and Security, 2025 -
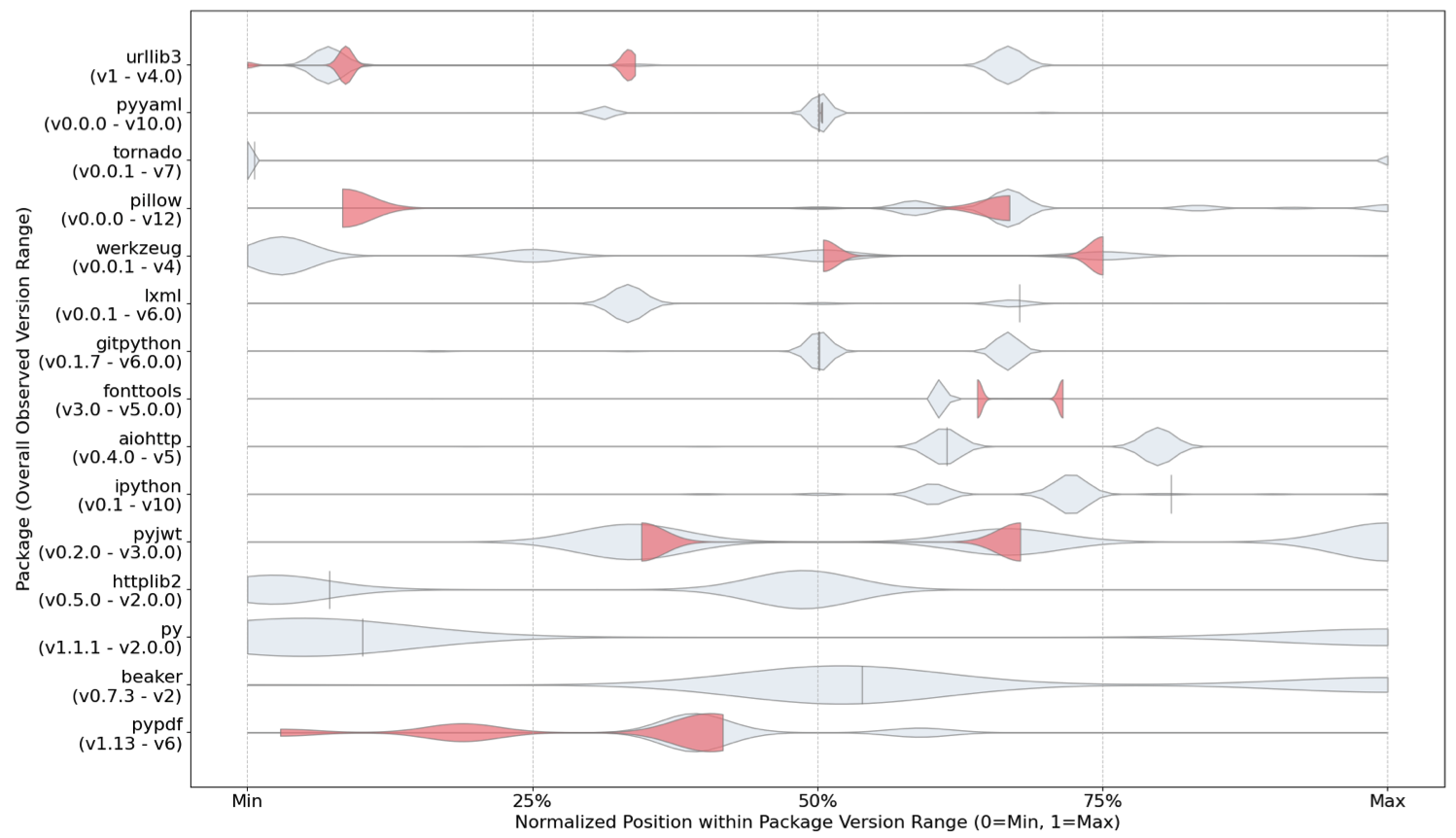 PyPitfall: Dependency Chaos and Software Supply Chain Vulnerabilities in PythonIn Proc. IEEE BigData (CyberHunt Workshop), 2025
PyPitfall: Dependency Chaos and Software Supply Chain Vulnerabilities in PythonIn Proc. IEEE BigData (CyberHunt Workshop), 2025
2024
-
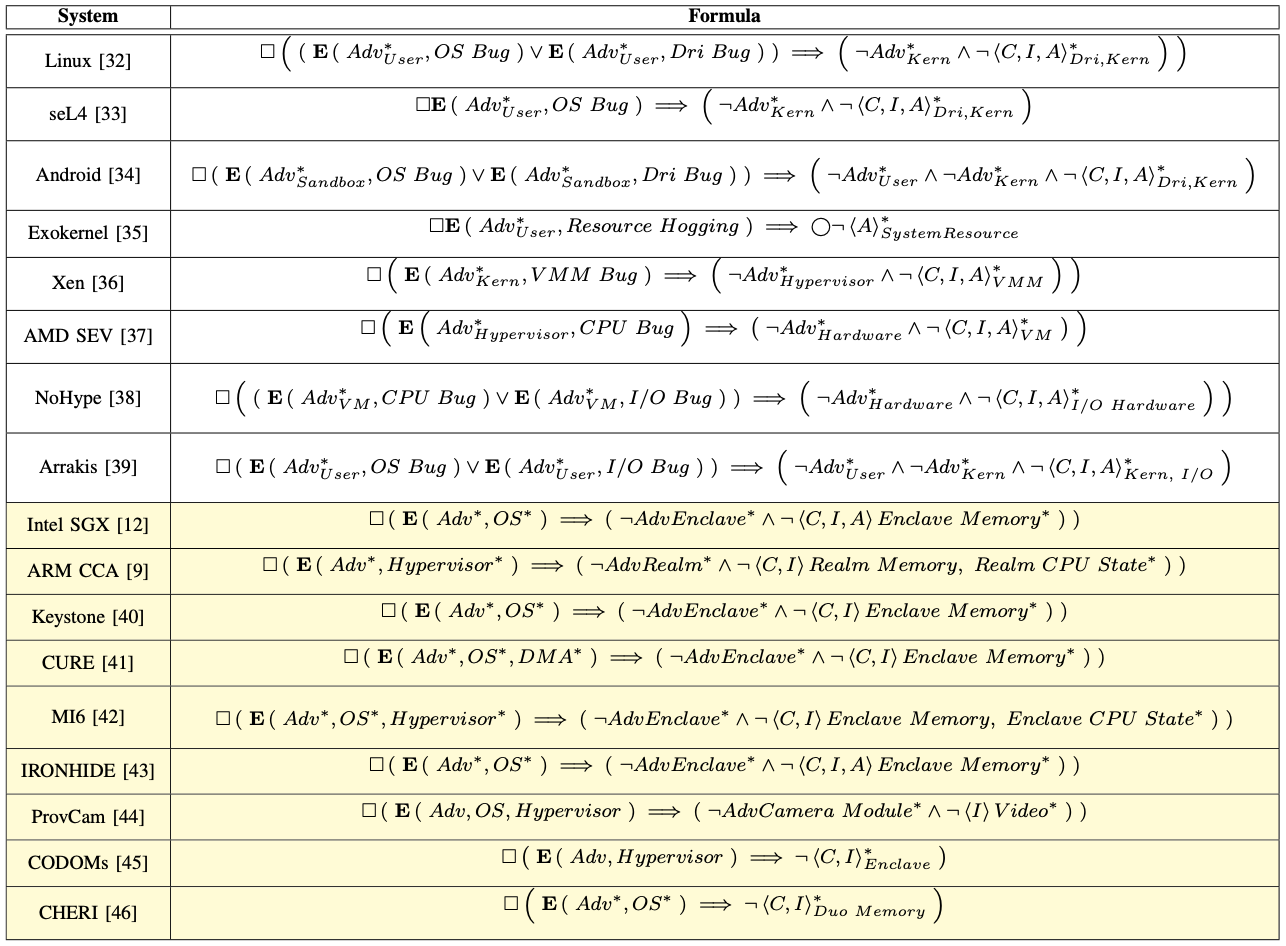 Formal Trust and Threat Modeling Using Large Language ModelsIn Proc. ACSAC Workshop on AI for Cyber Threat Intelligence (WAITI), 2024
Formal Trust and Threat Modeling Using Large Language ModelsIn Proc. ACSAC Workshop on AI for Cyber Threat Intelligence (WAITI), 2024
2023
-
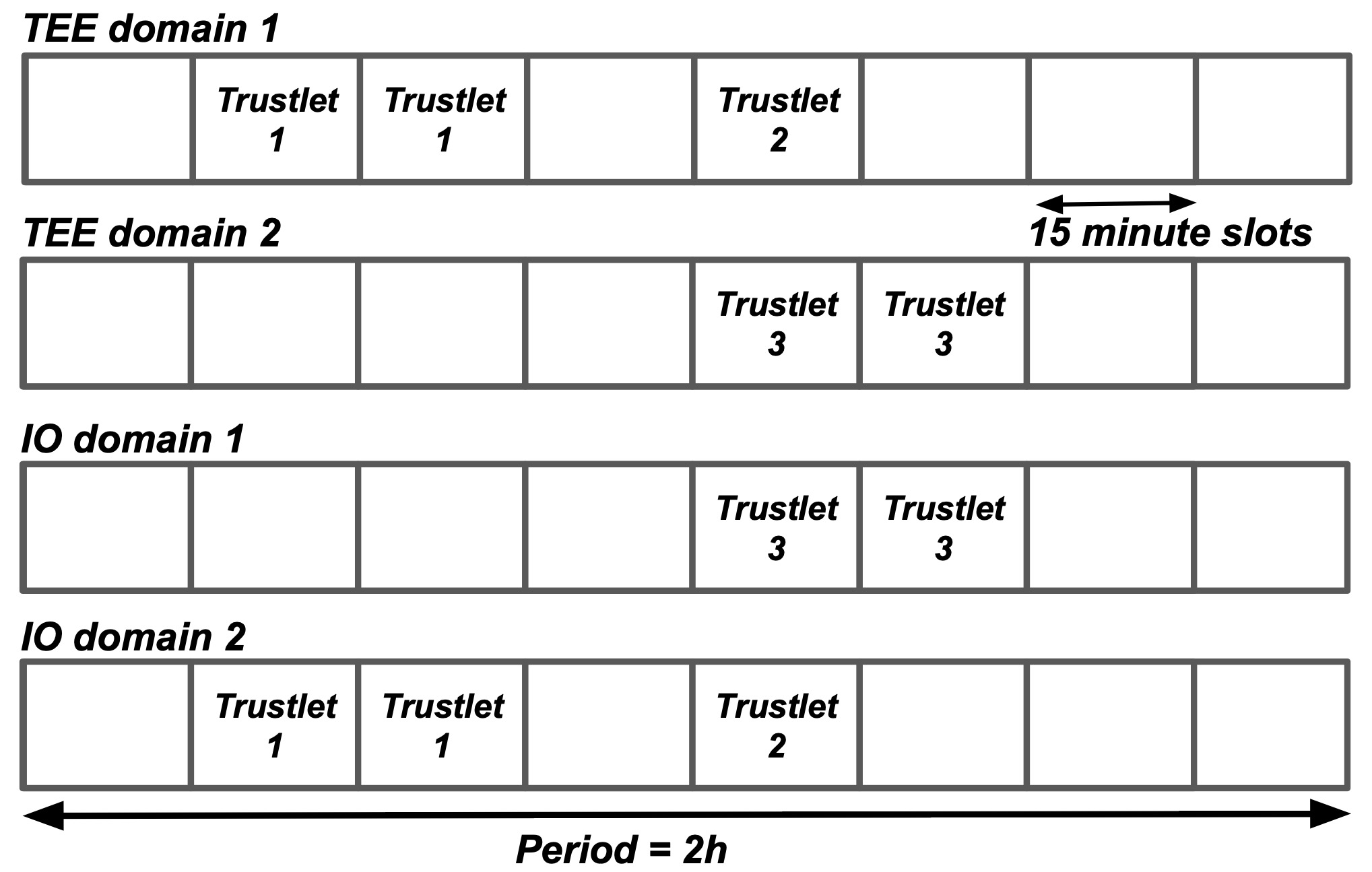
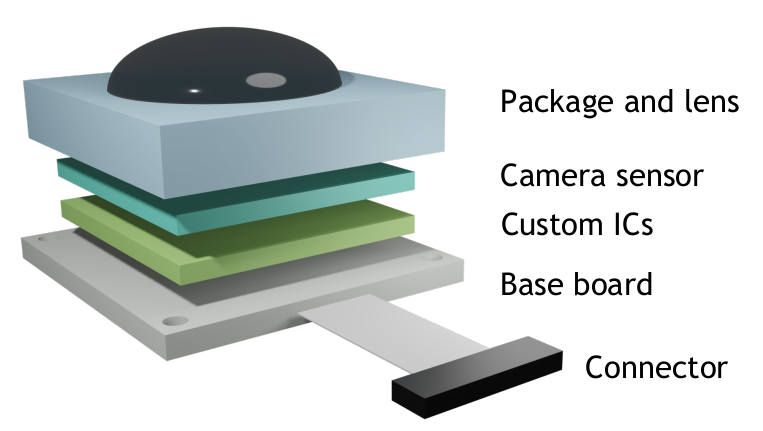
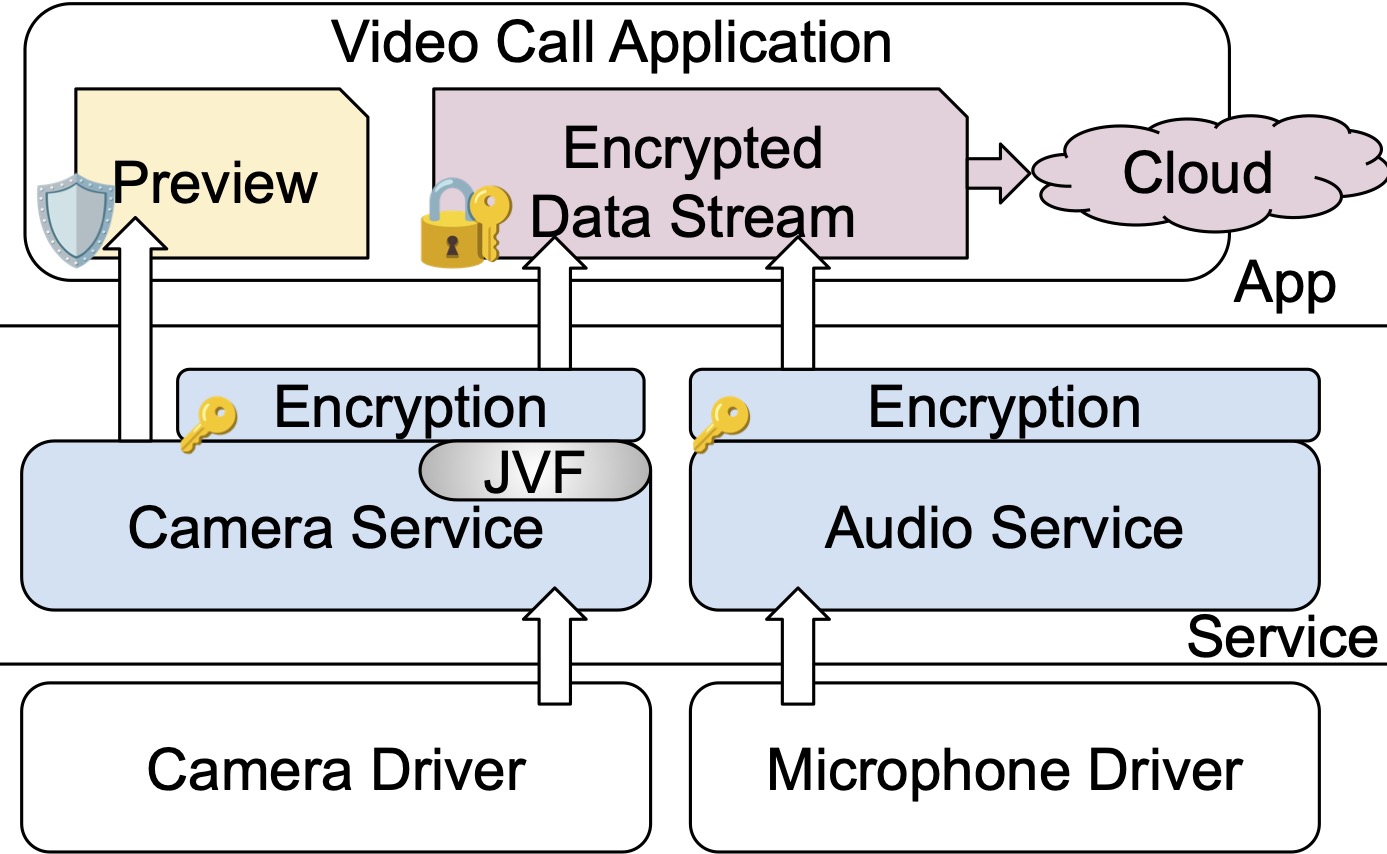
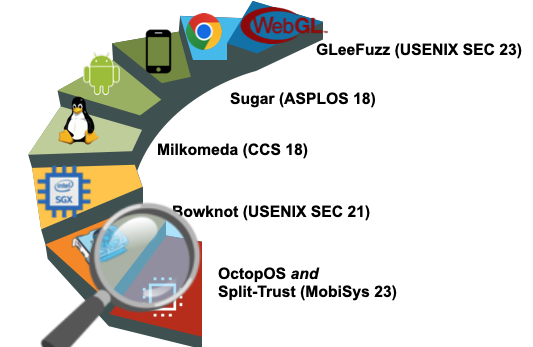
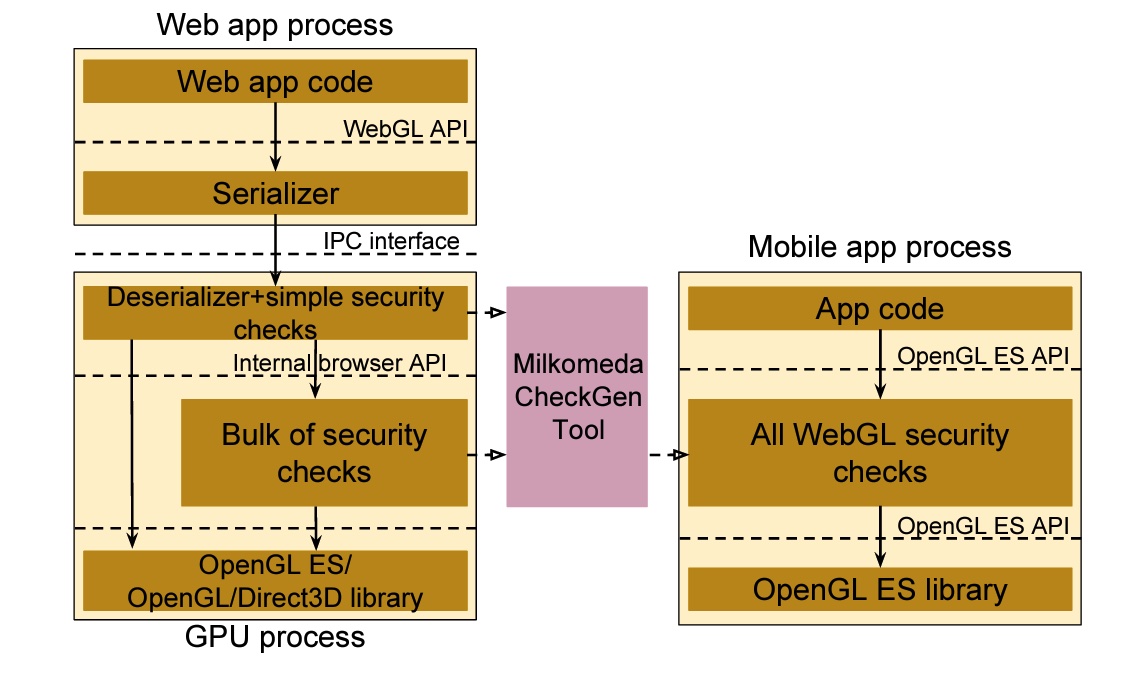
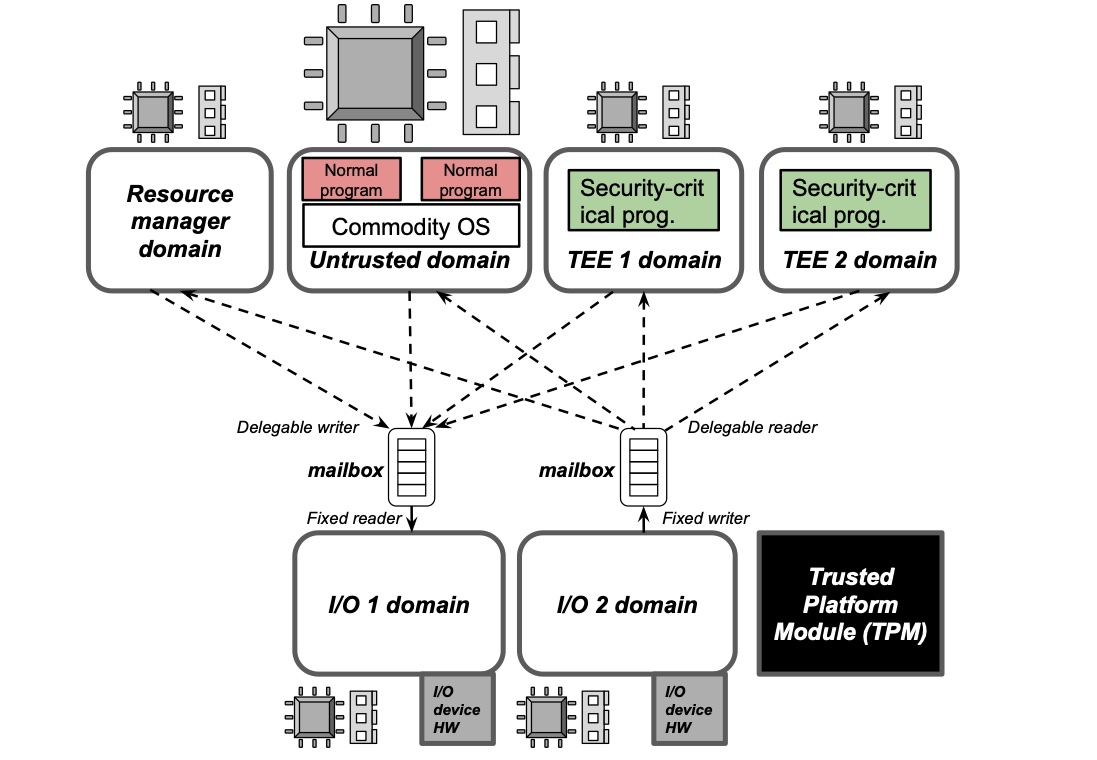 Minimizing a Smartphone’s TCB for Security-Critical Programs with Exclusively-Used, Physically-Isolated, Statically-Partitioned HardwareIn Proc. ACM MobiSys, 2023 🏆Best Artifact Award
Minimizing a Smartphone’s TCB for Security-Critical Programs with Exclusively-Used, Physically-Isolated, Statically-Partitioned HardwareIn Proc. ACM MobiSys, 2023 🏆Best Artifact Award -
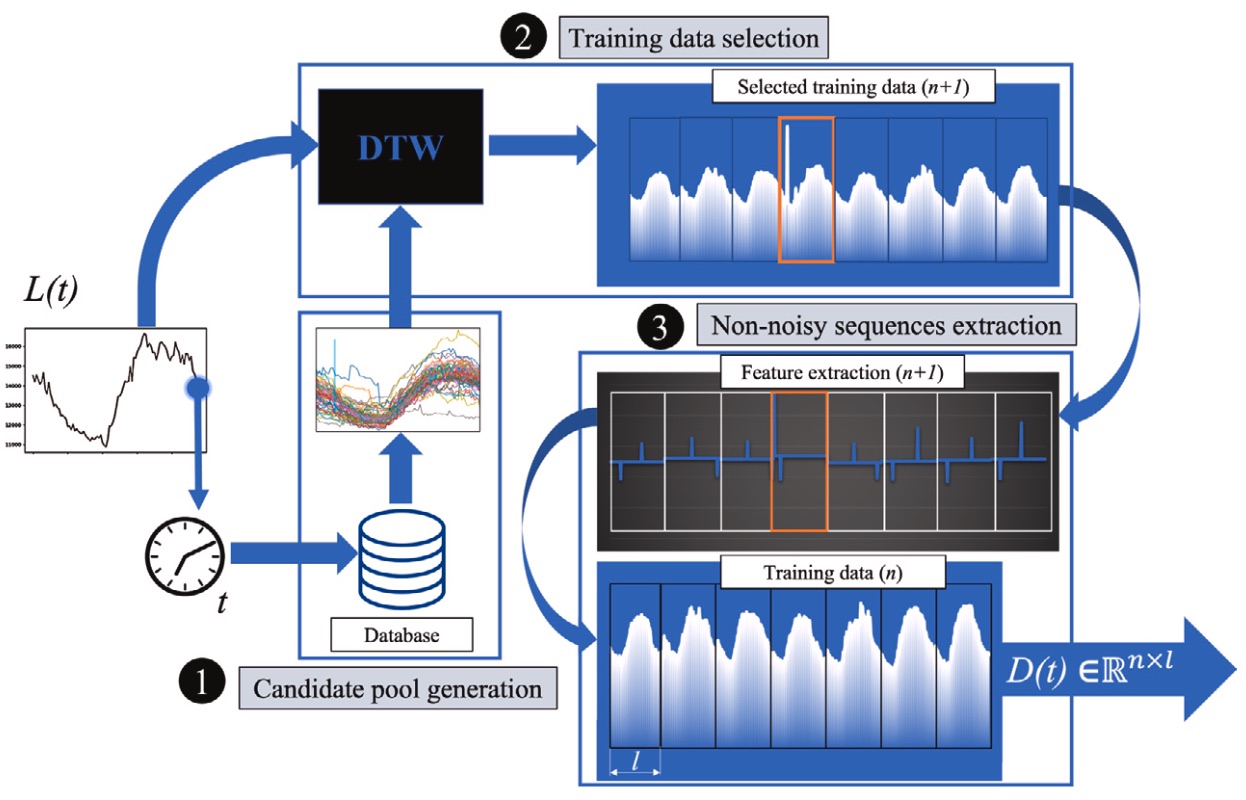 A real-time electrical load forecasting and unsupervised anomaly detection frameworkApplied Energy, 2023
A real-time electrical load forecasting and unsupervised anomaly detection frameworkApplied Energy, 2023